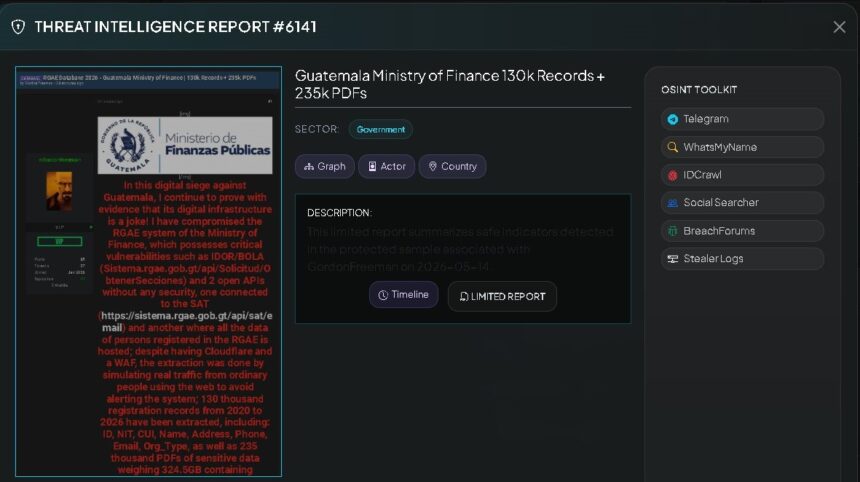
An alert released this Thursday, May 14, by the specialized cybersecurity account VECERT Analyzer warns of an alleged computer attack against the General Registry of State Acquisitions (RGAE), of the Ministry of Public Finance (Minfin), which would have compromised thousands of sensitive files and records.
According to the publication, the actor identified as “GordonFreeman”, linked to the LAT4MFUCK3RS group, claimed full access to the RGAE system by exploiting vulnerabilities in application programming interfaces (API), with which he would have evaded perimeter protection systems and extracted information from suppliers and people registered on the state platform.
The warning indicates that 130 thousand records corresponding to the period 2020-2026 would have been exfiltrated, in addition to 235 thousand PDF files, equivalent to 324.5 GB of information.
Among the data allegedly compromised are full names, Tax Identification Number (NIT), Unique Identification Code (CUI), addresses, telephone numbers and emails.
Documents such as university degrees, copies of DPI, invoices from the Superintendency of Tax Administration (SAT), tax certificates, business licenses, notarial deeds, bank account statements, financial balances and administrative contracts are also mentioned.
The specialized account indicated that the attacker would have taken advantage of vulnerabilities of the IDOR/BOLA type, related to improper access to internal sections of requests, as well as endpoints allegedly exposed without authentication.
VECERT Analyzer recommended that the Ministry of Finance immediately audit and close the compromised APIs, strengthen authentication mechanisms and apply controls under the principle of least privilege.
The publication also warned about possible risks of identity theft, phishing and extortion, due to the exposure of personal and financial documents.
So far, the Ministry of Finance has only reported that it verifies the veracity of the warning.
Context of cyber attacks in Guatemala
The alert occurs amid a series of cybersecurity incidents recorded in Guatemala during April 2026, which affected public institutions and higher education centers.
Among the actors mentioned in different attacks are “Gordon Freeman”, “MrGoblinciano” and “NemorisHacking”.
The first reported case occurred on April 7, when the General Directorate of Arms and Ammunition Control (Digecam) suffered an attack that allowed access to information from about 18 thousand users.
On April 21, 2026, Otto Rosito, director of Digecam, stated that they identified the hacker “Gordon Freeman” as responsible, who would have carried out similar actions in other Latin American countries.
They point out weaknesses in state systems
In the midst of these incidents, journalist and researcher Luis Assardo released on April 15 an analysis of vulnerabilities in state portals.
According to the evaluation, carried out on 134 websites of the Government of Guatemala:
- 64% obtained a D grade
- 87% lack security policies
- 92% allow access without encryption
- Attack on the Your Employment portal
On April 27, the Your Employment portal, of the Ministry of Labor and Social Security (Mintrab), was also the subject of a computer attack.
According to reports released at the time, more than 200,000 records and 40 GB of information were extracted, including resumes, DPI, contacts, and employment and salary history.
Luis Assardo indicated that day that the portal server still accepted connections using the TLS 1.0 and TLS 1.1 protocols, considered obsolete since 2020, and that it did not implement basic protection mechanisms such as Content-Security-Policy or HSTS.
Mintrab confirmed the incident and noted that it originated from an old API, which had already been corrected.
Subsequently, “Gordon Freeman” would have demanded the payment of two bitcoins – equivalent to about Q1.2 million – in exchange for not selling information allegedly obtained in attacks against Guatemalan institutions.
Universities also reported incidents
That same April 27, violations were reported at the University of San Carlos de Guatemala (Usac) and at the Rafael Landívar University (URL).
In the case of the Usac, it was alerted about the exposure of financial information from the Integrated Financial Information System (SIIF), including payroll data, CUI and banking information.
Marco Fuentes, head of the Data Processing Department of the USAC, stated on April 27, 2026 that a cyber attack was registered, although he assured that the systems, services and databases were not altered or manipulated.
In parallel, the leak of 84,620 photographs and personal data of students and teachers at the URL was reported.
The university reported on April 28, 2026 that it activated its internal protocols after learning of the incident and added that there was no evidence of structured, massive or systematic access to sensitive data.
*Stay up to date with the Now newsletter. Key information at the moment it happens. Subscribe here.